When setting up a check printing environment for a client, I ran into an issue where even though I changed the /etc/cupsd.conf file to listen on port 443, the service would not actually start!
Why not use the CUPS default port 631? Simple answer – too many of the client’s Palo Alto firewalls were configured to block IPP printing and since we were under a tight schedule, we could not afford to be held back by this. The client opted to instead run the services on 443 and thus take this element out of the picture when it came to testing the printing services on their end. So we had to make CUPS run on 443 instead of 631.
Upon reading some guides online, they seemed to indicate that CUPS could listen on any port and any interface as long as it is specified in the configuration file.
# Only listen for connections from the local machine. Listen 443 Listen /var/run/cups/cups.sock
However, when I ran lsof -i -P, I could not see the CUPSD service running! If I changed the configuration back to port 631 and restarted the service, I would see it come up.
[oraerpprntsvc@dmz-print1 ~]$ sudo lsof -i -P COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME systemd 1 root 47u IPv4 34335 0t0 TCP *:111 (LISTEN) systemd 1 root 48u IPv4 34336 0t0 UDP *:111 sshd 6292 root 3u IPv4 41258 0t0 TCP *:22 (LISTEN) master 6663 root 13u IPv4 42810 0t0 TCP localhost:25 (LISTEN) dnsmasq 6768 nobody 3u IPv4 43160 0t0 UDP *:67 dnsmasq 6768 nobody 5u IPv4 43163 0t0 UDP dmz-print1.localdomain:53 dnsmasq 6768 nobody 6u IPv4 43164 0t0 TCP dmz-print1.localdomain:53 (LISTEN) chronyd 6836 chrony 1u IPv4 43777 0t0 UDP localhost:323 cupsd 8682 root 9u IPv4 58443 0t0 TCP *:631 (LISTEN)
I started poking around and discovered that SELinux was enabled:
[oraerpprntsvc@dmz-print1 ~]$ getenforce Enforcing
I am not as well versed in Linux as I wish I would be, and having not worked in an environment where SELinux was in use, I admittedly had to do some googling.
I located this fine article about running SSHD on Port 443 and it helped me realize that I needed to make some changes to the SELinux port labeling policies. See, SELinux adds additional security and prevents services from running on ports other than what is defined in the master policy.
In order to bring up a list of services allowed to use port 443 (normally called HTTPS)
[oraerpprntsvc@dmz-print1 ~]$ sudo semanage port -l | grep 443 http_port_t tcp 80, 81, 443, 488, 8008, 8009, 8443, 9000 pki_ca_port_t tcp 829, 9180, 9701, 9443-9447 pki_kra_port_t tcp 10180, 10701, 10443-10446 pki_ocsp_port_t tcp 11180, 11701, 11443-11446 pki_tks_port_t tcp 13180, 13701, 13443-13446
The solution suggested by the guide was to add the tcp port 443 for the SSH_PORT_T configuration. Since we actually want to change the port for CUPS, we just replace SSH_PORT_T with IPP_PORT_T in the command.
[oraerpprntsvc@dmz-print1 ~]$ semanage port -m -t ipp_port_t -p tcp 443
After running the command and verifying that port tcp 443 was added to the allowed list for IPP (CUPS), we restart the service…
[oraerpprntsvc@dmz-print1 ~]$ sudo semanage port -l | grep ipp ipp_port_t tcp 443, 631, 8610-8614 ipp_port_t udp 631, 8610-8614 [oraerpprntsvc@dmz-print1 ~]$ sudo systemctl restart cups
We can observe that CUPS now shows up as listening on port 443:
[oraerpprntsvc@dmz-print1 ~]$ sudo lsof -i -P COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME systemd 1 root 47u IPv4 34335 0t0 TCP *:111 (LISTEN) systemd 1 root 48u IPv4 34336 0t0 UDP *:111 sshd 6292 root 3u IPv4 41258 0t0 TCP *:22 (LISTEN) master 6663 root 13u IPv4 42810 0t0 TCP localhost:25 (LISTEN) dnsmasq 6768 nobody 3u IPv4 43160 0t0 UDP *:67 dnsmasq 6768 nobody 5u IPv4 43163 0t0 UDP dmz-print1.localdomain:53 dnsmasq 6768 nobody 6u IPv4 43164 0t0 TCP dmz-print1.localdomain:53 (LISTEN) chronyd 6836 chrony 1u IPv4 43777 0t0 UDP localhost:323 cupsd 8682 root 9u IPv4 58443 0t0 TCP *:443 (LISTEN)
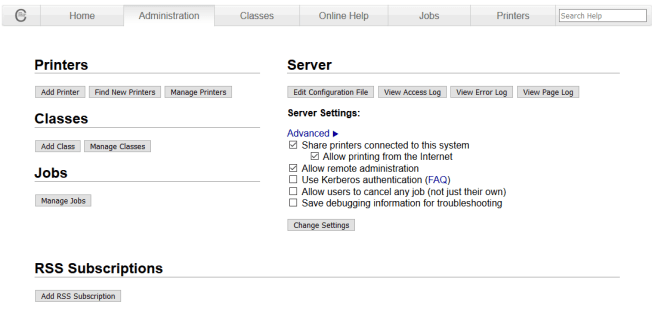
A quick check in the browser verifies that the service is correctly listening and accepting HTTPS/IPPS traffic.
That’s it! We are done.